Articles
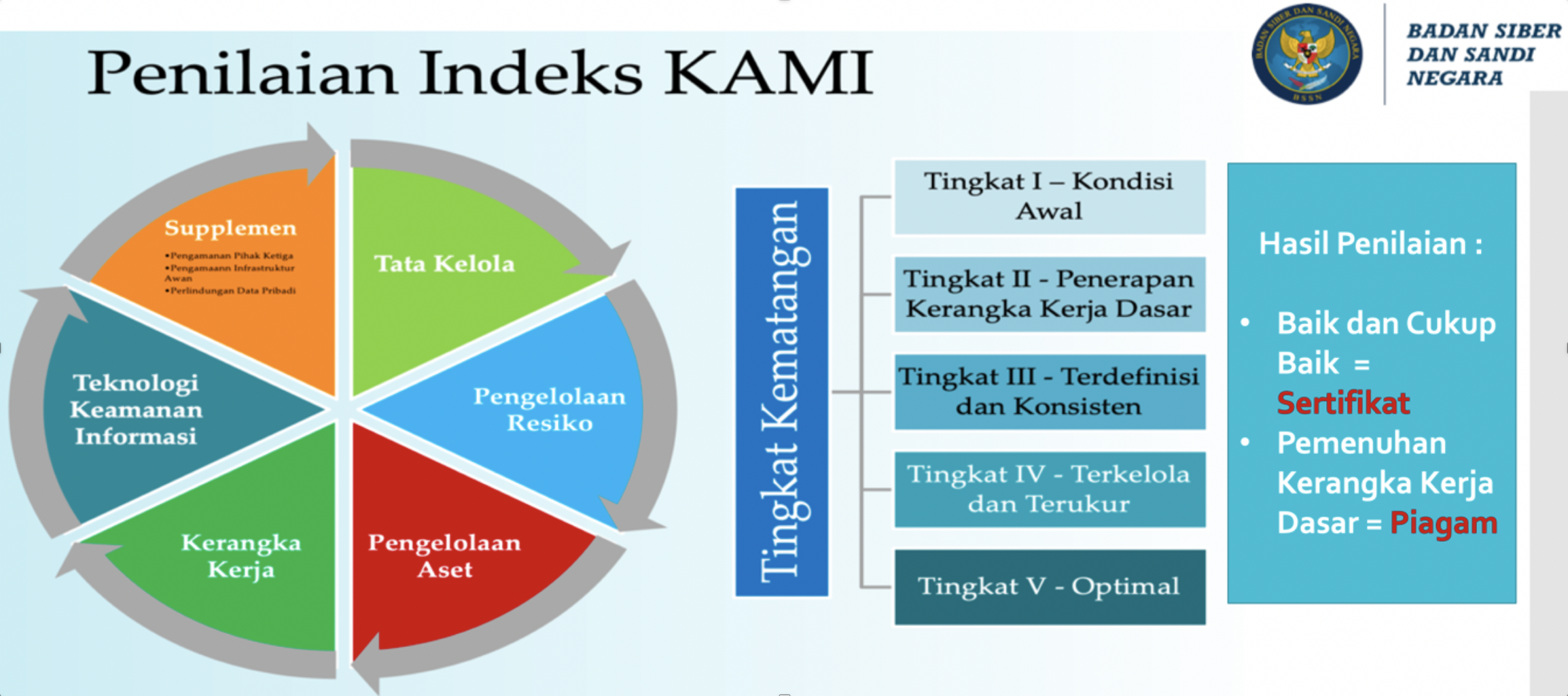
Information Security Risk Measurement Using Information Security Index (KAMI) at the Information Technology and Database Center
90-95 Pages
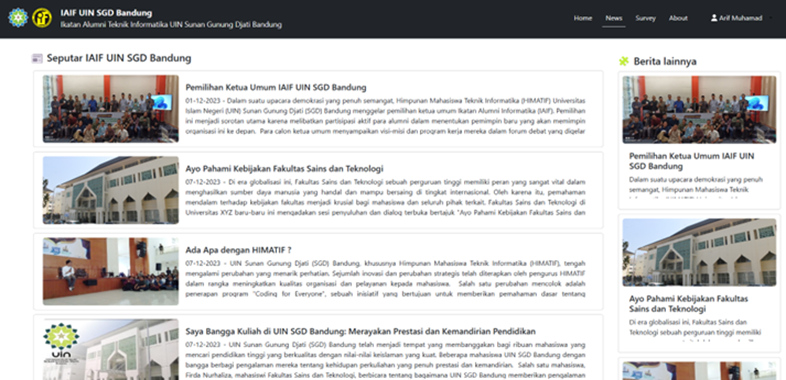
Designing a Website for the Alumni Association using Software Development Life Cycle
96-108 Pages
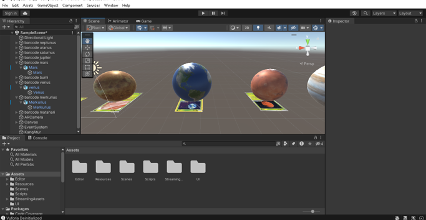
Augmented Reality (AR) Solar System Objects Based on Marker-Based 3D
109-115 Pages
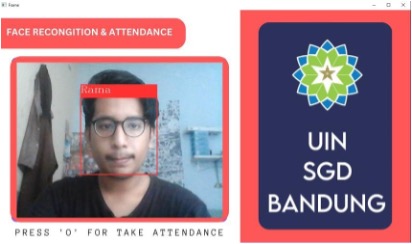
Attendance System Face Recognition Using Convolutional Neural Network (CNN)
116-121 Pages
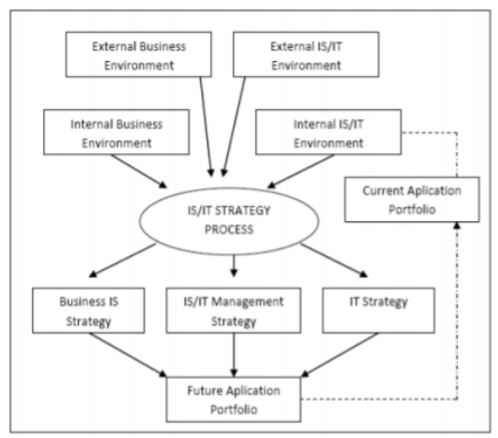
Strategic Information System Planning at UMKM in Padalarang Village using Ward and Peppard Methods
122-129 Pages